A sophisticated malware known as ViperSoftX has been observed to be distributed as e-books via torrent.
“A notable aspect of the current ViperSoftX variant is that it uses the Common Language Runtime (CLR) to dynamically load and execute PowerShell commands, thereby creating a PowerShell environment in AutoIt for operations,” Trellix security researchers Mathanraj Thangaraj and Sijo Jacob said.
“Using the CLR, ViperSoftX can seamlessly integrate PowerShell functionality, allowing it to perform malicious functions while evading detection mechanisms that might otherwise flag standalone PowerShell activity.”
Initially revealed Fortinet in 2020 ViperSoftX is known for its ability to extract sensitive information from compromised Windows hosts. Over the years, malware has become a relevant example of how threat actors are constantly updating their tactics in an attempt to stay stealthy and bypass defenses.
An example of this is the increasing sophistication and adoption of advanced anti-analysis techniques such as byte remapping and web browser communication blocking, as documented by Trend Micro in April 2023.
Back in May 2024, there were malicious campaigns loan funds ViperSoftX as delivery vehicle to distribute Quasar RAT and another information stealer called TesseractStealer.
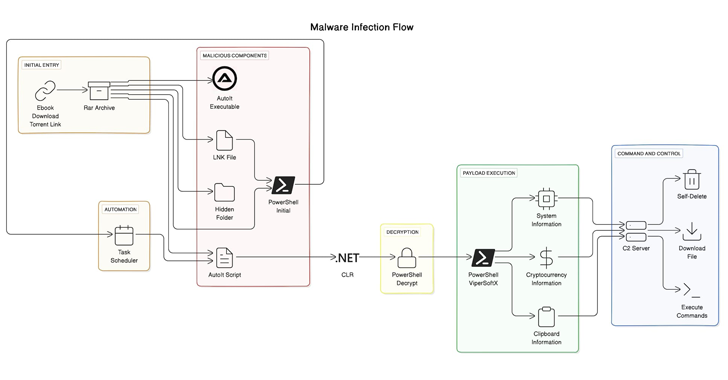
Attack chains that distribute malware are known to use cracked software and torrent sites, but using e-books is a new approach. The alleged RAR eBook archive file contains a hidden folder as well as a fraudulent Windows shortcut file that pretends to be a benign document.
Executing the hotkey file initiates a multi-step infection sequence that begins by extracting PowerShell code that reveals a hidden folder and configures a save on the system to run an AutoIt script, which in turn interacts with the .NET CLR framework to decrypt and run a secondary PowerShell script. which is ViperSoftX.
“AutoIt does not support the .NET Common Language Runtime (CLR) by default,” the researchers said. “However, user-defined language functions (UDS) offer a gateway to the CLR library, giving attackers access to the vast power of PowerShell.”

ViperSoftX collects system information, searches for cryptocurrency wallets through browser extensions, grabs clipboard contents, and dynamically loads and runs additional payloads and commands based on responses received from a remote server. It also comes with self-delete mechanisms to defy detection.
“One of the defining features of ViperSoftX is its skillful use of the Common Language Runtime (CLR) to orchestrate PowerShell operations within the AutoIt environment,” the researchers said. “This integration allows malicious functionality to be executed seamlessly, evading the detection mechanisms that typically flag standalone PowerShell activity.”
“Furthermore, ViperSoftX’s ability to patch the Anti-Malware Scanning Interface (AMSI) before executing PowerShell scripts underscores its determination to bypass traditional security measures.”