Cybersecurity researchers have warned of a new campaign aimed at Portuguese users in Brazil with a trial version of commercial software for remote monitoring and management (RMM) since January 2025.
“In the SPAM message used Brazilian Electronic Account System – Note In the report on Thursday.
Attack networks start with a specially designed spam -electronic letters that claim that they come from financial institutions or cellphone media, preferred accounts or payable payments to fool users to press Bogus Dropbox links indicating the binary installer for the RMM instrument.
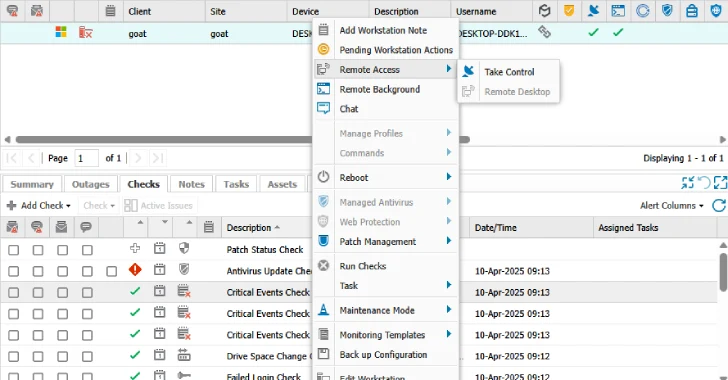
Two notable RMM tools observed N-IT RMM Remote Access and PDQ ConnectGiving the attackers the ability to read and write files in a remote file system.
In some cases, the actors threatens use the distant capabilities of these agents to download and install additional RMM software, such as Screenconnect after the initial compromise.
Based on the common recipients, it was found that the company is mainly focused on CEAs and financial and human resources in several fields, including some educational and government agencies.
Also with high confidence, the activity of the original access broker (IAB), which abuses free trial periods related to different RMM programs to gain unauthorized access. Since then, N-Fave has taken measures to shut down the affected accounts.
“The abuse of opponents by commercial RMM tools has invariably increased in recent years,” Venorer said. “These tools are of interest to the threat to the subjects as they are usually signed by digital organizations and are quite noticeable back.”
“They also have virtually no costs in the software and infrastructure, as all this is usually provided in the application for a trial version.”
Development occurs against the background of various phishing campaigns that are designed for the parties of modern protection and distribute a wide range of malware or collecting victims –
- A company conducted by a South American cybercrime group called Hive0148 for distribution Grandoreiro Banking Trojan for users in Mexico and Costa -Cric.
- A company that uses the legal file distribution service named Obtain bypass security protection and send users to links to hosting malware
- A company that uses Baits with order sales For delivery Form of books Malicious software using the Microsoft Word document that is sensitive to many years of lack of equation editor (Cve-2017-1188)
- A company aimed at organizations in Spain, Italy and Portugal, using accounts related to trayan -based Java, called Rat Rat which can execute deleted commands, log keys, screenshots and steal sensitive data
- The company that used Legitimate application 2FA tycoon Fix users’ accounts under the guise of viewing the “new agreement”
- Companies that relate Coded JavaScript in SVG files, links registered in BOOBY in PDF, attachments, dynamic phishing URLs that are displayed in the files that are in files
- Companies that abuse Cloudflare Tunning Function TryCloudflare deploy malicious software like Assembly
“The attackers are constantly developing tactics to bypass modern email safety and final points, making the detection and mitigation of phishing attempts more complicated,” Intezer Guri’s researcher said last month. “And despite the progress in cybersecurity instruments, many phishing companies are still successfully achieving users’ mailboxes.”