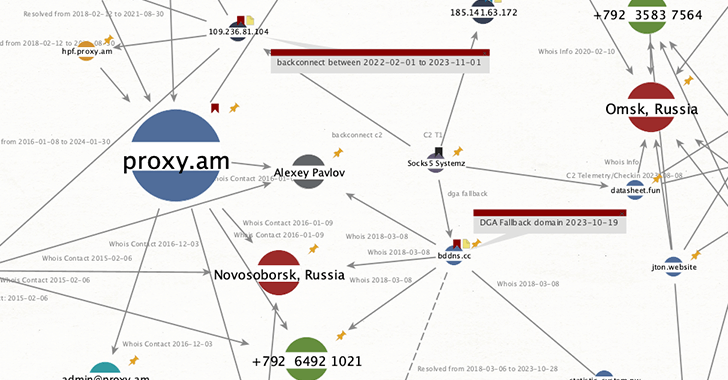
Calling a malicious botnet Socks5Systemz according to Bitsight’s new findings, a proxy service called PROXY.AM is operating.
“Malware proxies and services allow other types of criminal activity to add uncontrollable levels of anonymity to threat actors so they can perform all kinds of malicious activities by exploiting chains of victim systems,” the company’s security research team said in an analysis published last week.
The disclosure comes just weeks after Black Lotus Labs’ team with Lumen Technologies revealed that systems compromised by another malware known as Ngioweb are being used as residential proxies for NSOCKS.
Originally touted in the cybercrime underground back in March 2013, Socks5Systemz was previously documented BitSight as deployed as part of cyberattacks aimed at spreading PrivateLoader, SmokeLoader and Amadey.
The primary purpose of the malware is to turn compromised systems into proxy exit nodes that are then advertised to other actors, usually cybercriminals, who seek to hide the source of their attacks. The illegal proxy service has been around since 2016.
The countries with the highest number of infected hosts are India, Indonesia, Ukraine, Algeria, Vietnam, Russia, Turkey, Brazil, Mexico, Pakistan, Thailand, Philippines, Colombia, Egypt, USA, Argentina, Bangladesh, Morocco, and Nigeria.
The size of the botnet is said to have increased to an average of 250,000 machines per day by January 2024, although current estimates range from 85,000 to 100,000. At the time of writing, PROXY.AM claims to have 80,888 proxy nodes , available from 31 countries.
“In December 2023, the threat actor lost control of Socks5Systemz V1 and had to rebuild the botnet from scratch with a completely different (command and control) infrastructure — which we call the Socks5Systemz V2 botnet,” Bitsight said, explaining the reason for the decline.
“Since Socks5Systemz is dropped by loaders (such as Privateloader, SmokeLoader or Amadey) stored on the system, new distribution campaigns have been used to replace old infections with new payloads.”
PROXY.AM (proxy(.)am and proxyam(.)one) markets itself as “elite, private and anonymous proxy servers” with prices ranging from $126 per month (unlimited package) to $700 per month (VIP package ).
The disclosure follows a Trend Micro report detailing ongoing attempts by threat actors to target misconfigured Docker Remote API servers using Gaffit botnet malware that helps conduct distributed denial-of-service (DDoS) attacks against targets of interest.
While Gafgyt has a track record of targeting vulnerable IoT devices, the malware’s use of weak SSH passwords and Docker instances indicates that its scope is expanding.
“We’ve noticed that attackers have targeted exposed, misconfigured remote Docker API servers to deploy malware by building a Docker container based on a legitimate ‘alpine’ Docker image,” security researcher Sunil Bharti said. “Along with the deployment of the Gafgyt malware, the attackers used the Gafgyt botnet malware to infect the victim.”
Incorrect cloud configurations proved be an attractive attack surface for threat actors deploy a cryptocurrency miner, steal dataand co-opt them into botnets for DDoS attacks.
According to a new empirical analysis conducted by a team of researchers from Leiden University and Delft Institute of Technology, 215 cases of exposure of sensitive credentials were found that could potentially give attackers unauthorized access to services such as databases, cloud infrastructure and third-party APIs.
The majority of instances were located in the United States, India, Australia, the United Kingdom, Brazil, and South Korea and spanned multiple sectors such as information technology (IT), retail, finance, education, media, and healthcare.
“The findings highlight the urgent need for improved system administration and vigilance to prevent data breaches,” Modat Team said. “The impact of these secrets being leaked can be enormous, ranging from complete control of an organization’s security infrastructure to impersonation and penetration of protected cloud infrastructure.”