Taiwanese manufacturing, healthcare and information technology businesses have been targeted by a new SmokeLoader malware distribution campaign.
“SmokeLoader is well known for its versatility and advanced evasion techniques, and its modular design allows for a wide range of attacks” – Fortinet FortiGuard Labs said in a report shared with The Hacker News.
“While SmokeLoader mainly serves as a loader to deliver other malware, in this case it is carrying out the attack itself by loading plugins from its (command and control) server.”
SmokeLoaderfirst touted on cybercrime forums in 2011, the malware downloader is primarily designed to execute secondary payloads. In addition, it has the ability to download additional modules that extend its own functionality to steal data, launch distributed DDoS attacks, and mine cryptocurrency.
“SmokeLoader detects analysis environment, generates spoofed network traffic, and obfuscates code to avoid detection and thwart analysis,” Extensive Zscaler ThreatLabz Malware Analysis noted.
“The developers of this malware family are consistently expanding its capabilities, introducing new features and using obfuscation techniques to thwart analysis.”
After that, SmokeLoader activity dropped significantly Operation Endgame.a Europol-led effort that dismantled the infrastructure tied to several malware families, such as IcedID, SystemBC, PikaBot, SmokeLoader, Bumblebee, and TrickBot in late May 2024.
More than 1,000 C2 domains associated with SmokeLoader have been dismantled and more than 50,000 infections have been remotely removed. However, the malware continues to be used by threat groups to distribute payloads across the new C2 infrastructure.
This, trans Zscalerin large part because of the many hacked versions that are publicly available on the Internet.
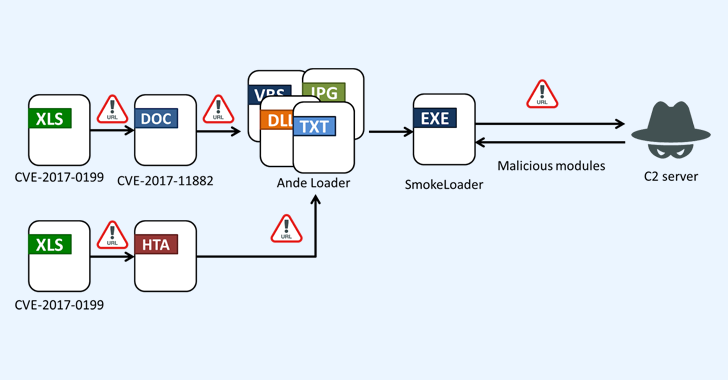
The starting point of the latest attack chain discovered by FortiGuard Labs is a phishing email containing a Microsoft Excel attachment that, when executed, exploits long-standing security flaws (such as CVE-2017-0199 and CVE-2017-11882) to remove the malware bootloader it invokes Ande Loaderwhich is then used to deploy SmokeLoader on the compromised host.
SmokeLoader consists of two components: a stacker and a main module. While the stager’s purpose is to decode, extract, and inject the main module into the explorer.exe process, the main module is responsible for creating persistence, communicating with the C2 infrastructure, and processing commands.
The malware supports several plugins that can steal login and FTP credentials, email addresses, cookies, and other information from web browsers, Outlook, Thunderbird, FileZilla, and WinSCP.
“SmokeLoader executes its attack using its plugins instead of loading a completed file for the final stage,” Fortinet said. “This shows the flexibility of SmokeLoader and highlights that analysts need to be careful even when looking at such known malware.”