Cybersecurity researchers have discovered a new malicious campaign that uses a technique called Bring Your Own Vulnerable Driver (BEUD) to remove the protection and eventually gain access to the infected system.
“This malware takes a more sinister path: it removes the legitimate Avast Anti-Rootkit driver (aswArPot.sys) and manipulates it to execute its destructive program,” Trellix Security Researcher Trishaan Kalra said in an analysis published last week.
“The malware uses the deep access provided by the driver to stop security processes, disable security software, and seize control of the infected system.”
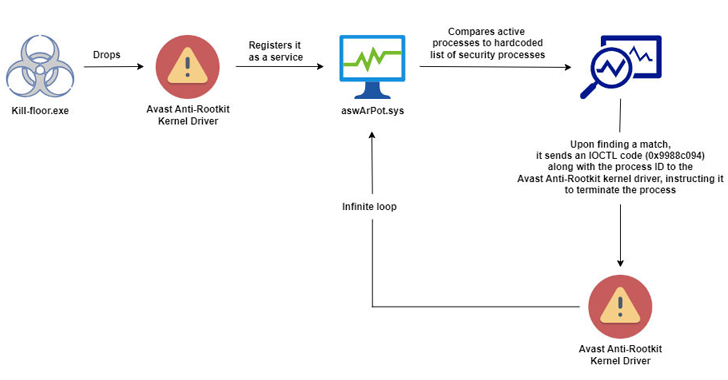
The starting point of the attack is an executable file (kill-floor.exe) that removes the legitimate Avast Anti-Rootkit driver, which then registers itself as a service using Service Control (sc.exe) to perform its malicious activities.
Once the driver is launched, the malware gains access to the system at the kernel level, allowing it to kill a total of 142 processes, including those related to security software, which would otherwise trigger an alarm.
This is achieved by taking snapshots of actively running processes on the system and matching their names to a hard-coded list of processes to kill.
“Because kernel-mode drivers can override user-mode processes, the Avast driver is able to kill processes at the kernel level, effortlessly bypassing the intrusion protection mechanisms of most antivirus and EDR solutions,” Kalra said.
The exact initial access vector used to remove the malware is currently unclear. It is also unknown how widespread these attacks are and who is being targeted.
However, BYOVD attacks are becoming an increasingly common method used by threat actors deploy ransomware in recent years when they reuse signed but faulty drivers to bypass security controls.
Earlier this May, Elastic Security Labs revealed details of the GHOSTENGINE malware company that used the Avast driver to disable security processes.