Ukraine’s Computer Emergency Response Team (CERT-UA) has detailed a new malicious electronic campaign targeting government agencies, businesses and military structures.
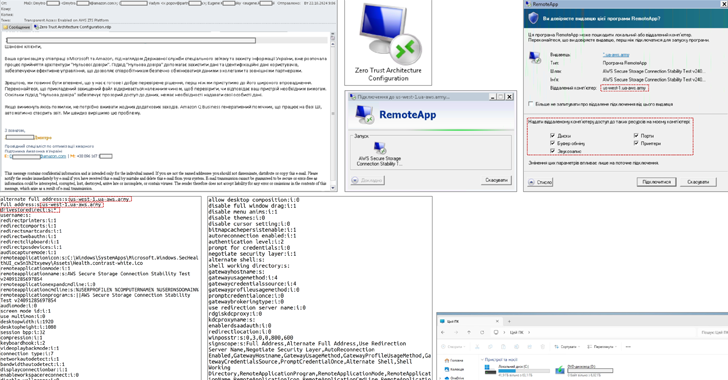
“Messages use the appeal of integrating popular services like Amazon or Microsoft and implementing a zero-trust architecture,” CERT-UA said. “These emails contain attachments in the form of Remote Desktop Protocol (‘.rdp’) configuration files.”
Once executed, RDP files establish a connection to a remote server, allowing threat actors to remotely access compromised nodes, steal data, and install additional malware for subsequent attacks.
Infrastructure preparations for this activity are believed to have been underway since at least August 2024, with the agency saying it is likely to spill over from Ukraine to other countries.
CERT-UA attributed the campaign to a threat actor it tracks as UAC-0215. Amazon Web Service (AWS) in its own advisory linked it to a Russian nation-state hacking group known as APT29.
“Some of the domain names they used tried to trick targets into believing the domains were AWS domains (they weren’t), but Amazon wasn’t the target, nor was the group after AWS customer credentials,” CJ Moses, Amazon’s Chief Information Officer. security officer, said. “In contrast, APT29 sought its targets’ Windows credentials via Microsoft Remote Desktop.”
The tech giant said it also seized domains the adversary was using to impersonate AWS to neutralize the operation. Some of the domains used by APT29 are listed below –
- ca-west-1.mfa-gov(.)cloud
- central-2-aws.ua-aws(.)army
- us-east-2-aws.ua-gov(.)cloud
- aws-ukraine.cloud
- aws-data.cloud
- aws-s3.cloud
- aws-il.cloud
- aws-join.cloud
- aws-meet.cloud
- aws-meetings.cloud
- aws-online.cloud
- aws-secure.cloud
- s3-aws(.)cloud
- s3-fbi(.)cloud
- s3-nsa(.)cloud, and
- s3-proofpoint(.)cloud
This event took place after CERT-UA also warned about a large-scale cyber attack aimed at stealing confidential information of Ukrainian users. The threat was cataloged under the alias UAC-0218.
The starting point of the attack is a phishing email containing a link to a mined RAR archive that claims to be invoices or payment details.
The archive contains a Visual Basic Script-based malware called HOMESTEEL designed to steal files with specific extensions (“xls”, “xlsx”, “doc”, “docx”, “pdf”, “txt”, “csv, ” “rtf,” “ods,” “odt,” “eml,” “pst,” “rar,” and “zip”) to a server controlled by the attacker.
“In this way, criminals can gain access to personal, financial and other sensitive data and use it for blackmail or theft” – CERT-UA said.
In addition, CERT-UA has wary with a Click Fix-a company designed to trick users into clicking malicious links embedded in email messages to remove a PowerShell script capable of establishing an SSH tunnel, stealing data from web browsers, and downloading and running the Metasploit penetration testing system.
Users who click on the link are taken to a fake reCAPTCHA verification page that prompts them to confirm their identity by clicking a button. This action copies a malicious PowerShell script (“Browser.ps1”) to the user’s clipboard and displays a popup with instructions for executing it using the Windows Run dialog.
CERT-UA said it has “medium confidence” that the campaign is the work of another Russian advanced persistent threat actor known as APT28 (aka UAC-0001).
Cyber attacks against Ukraine are taking place against the background of a the report from Bloomberg, which details how Russia military intelligence agency and the Federal Security Service (FSB) systematically attacked Georgia’s infrastructure and government in a series of digital intrusions between 2017 and 2020. Some of the attacks have been linked to Tower.