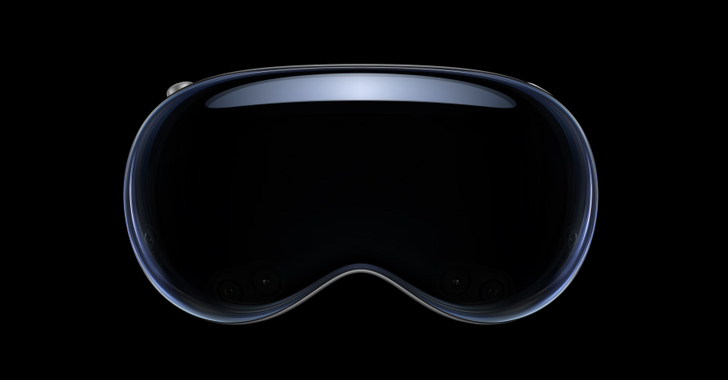
Details have emerged of a patched security flaw affecting Apple’s Vision Pro mixed reality headset that, if successfully exploited, could allow attackers to infer data entered on the device’s virtual keyboard.
Attack, dubbing GAZEploitwas assigned the CVE ID CVE-2024-40865.
“A New Attack That Can Infer Eye Biometrics from an Avatar Image to Recover Text Typed Using Gaze-Controlled Typing,” by a team of researchers at the University of Florida said.
“The GAZEploit attack exploits a vulnerability inherent in gaze-controlled text input when users share a virtual avatar.”
After a responsible disclosure, Apple fixed the issue in visionOS 1.3, released on July 29, 2024. The vulnerability was described as affecting a component called Presence.
“Virtual keyboard input can be output from Persona,” it said said in the security advisory, adding that it fixed the issue by “pausing Persona when the virtual keyboard is active.”
In a nutshell, researchers have discovered that it is possible to analyze the eye movements (or “gaze”) of a virtual avatar to determine what the user wearing the headset is typing on the virtual keyboard, effectively compromising their privacy.
As a result, a threat actor could hypothetically analyze virtual avatars shared via video calls, online dating apps, or live streaming platforms and remotely perform keystroke inference. This can then be used to extract sensitive information such as passwords.

The attack, in turn, is carried out using a supervised learning model that is trained on Persona recordings, eye aspect ratio (EAR), and gaze estimation to distinguish between typing sessions and other VR-related activities (such as watching movies or playing games) . ).
In the next step, gaze estimation directions on the virtual keyboard are mapped to specific keys to determine potential keystrokes in a way that also takes into account the location of the keyboard in virtual space.
“By remotely capturing and analyzing the video of the virtual avatar, an attacker can reconstruct the keys typed,” the researchers said. “Notably, the GAZEploit attack is the first known attack in this domain to use gaze leak information to remotely perform keystroke inference.”