Chinese-speaking users are being targeted by a “highly organized and sophisticated attack” campaign that is likely using phishing emails to infect Windows systems with Cobalt Strike payloads.
“The attackers were able to move sideways, establish persistence, and remain undetected on systems for over two weeks,” Securonix researchers Dan Yuzwick and Tim Peck said in a new report.
A secret company under a code name SLOW#STORM and not attributed to any known threat actor, begins with malicious ZIP files that, when unzipped, activate an infection chain that leads to the deployment of a suite of tools after being exploited on compromised systems.
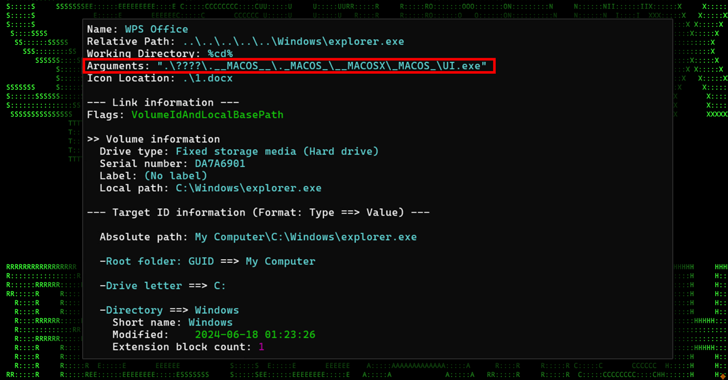
The ZIP archive contains a Windows Shortcut (LNK) file masquerading as a Microsoft Word file, “List of People Who Violated Remote Control Software Rules.docx.lnk”, which roughly translates to “List of People Who Violated Software Rules for remote control.”
“Given the language used in the decoy files, it is likely that certain China-related business or government sectors could be targeted, as both would employ people who adhere to the ‘remote control software regulations,'” the researchers said.
The LNK file acts as a conduit to run a legitimate Microsoft binary (“LicensingUI.exe”) that uses Sideloading DLL to execute a fake DLL (“dui70.dll”). Both files are part of a ZIP archive in a directory called “\安全手机\.__MACOS__\._MACOS_\__MACOSX\_MACOS_.” This attack was the first case of DLL sideloading via LicensingUI.exe.
The DLL file is a Cobalt Strike implant that allows persistent and covert access to the infected host when communicating with a remote server (“123.207.74(.)22”).
The remote access is said to have allowed the attackers to perform a number of practical actions, including deploying additional intelligence payloads and setting up proxy connections.
The infection chain is also notable for setting up a scheduled task to periodically execute a malicious executable called “lld.exe” that can run arbitrary shellcode directly in memory, thus leaving minimal traces on disk.
“Additionally, attackers allowed themselves to hide in the weeds of compromised systems by manually elevating the privileges of the built-in guest account,” the researchers said.
“This account, normally disabled and with minimal privileges, has been transformed into a powerful access point by adding it to a critical administrative group and giving it a new password. This backdoor allows them to maintain access to the system with minimal detection, as the Guest account is often not monitored as closely as other user accounts.”
The unknown threat actor then moved across the network using Remote Desktop Protocol (RDP) and credentials obtained with the Mimikatz password extraction tool, followed by setting up remote connections back to their management server (C2) from each of these machines.
The post-exploitation phase is also characterized by running several enumeration commands and using the BloodHound tool for Active Directory (AD) exploration, the results of which were then exfiltrated as a ZIP archive.

The ties to China are strengthened by the fact that all C2 servers are hosted in China by Shenzhen Tencent Computer Systems Company Limited. Also, most of the artifacts associated with the company come from China.
“Although there was no hard evidence linking this attack to any known APT groups, it was likely orchestrated by a sophisticated threat actor with experience using advanced exploit infrastructures such as Cobalt Strike and a wide range of other tools after exploitation,” the researchers note. concluded.
“The company’s sophistication is evident in its methodical approach to initial compromise, persistence, privilege escalation, and lateral network movement.”