In an operational security (OPSEC) breach, the operator behind a new information stealer called Styx Stealer leaked data from his own computer, including customer details, earnings information, nicknames, phone numbers and email addresses.
Styx Stealer, derived from Thief of phemedroneis capable of stealing browser data, Telegram and Discord instant messaging sessions, and cryptocurrency wallet information, according to an analysis by cybersecurity firm Check Point. It first appeared in April 2024.
“Styx Stealer is likely based on the source code of an older version of Phemedrone Stealer, which lacks some features that newer versions have, such as sending reports to Telegram, encrypting reports, and more,” the company said in a statement. noted.
“However, the creator of Styx Stealer added several new features: autorun, clipboard monitor and crypto clipper, additional sandbox evasion and anti-analysis methods, and re-implemented sending data to Telegram.”
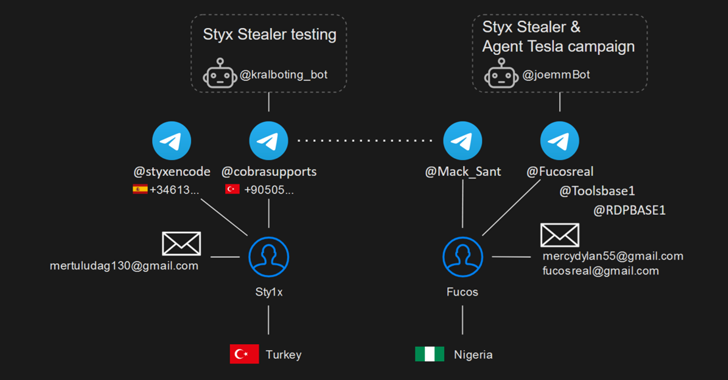
Licenses for the malware, advertised for $75 per month (or $230 for three months or $350 for a lifetime subscription) on a dedicated website (“styxcrypter(.)com”), require potential buyers to access a Telegram account (@styxencode) . It is linked to a Turkish threat actor who goes by the alias STY1X on cybercrime forums.
Check Point said it was able to identify a link between STY1X and a spam campaign in March 2024 that distributed the Agent Tesla malware targeting various sectors across China, India, the Philippines and the UAE. Agent Tesla’s activities were linked to a threat called Fucosreal, whose approximate location is in Nigeria.
This was made possible by STY1X debugging their machine with a Telegram bot token provided by Fucosreal. This fatal error allowed the cybersecurity company to identify 54 customers and 8 cryptocurrency wallets believed to be owned by STY1X, which were said to have been used to receive payments.
“This campaign is unique in that it uses the Telegram Bot API to steal data, using Telegram’s infrastructure instead of traditional command and control (C&C) servers, which are easier to detect and block,” Check Point said.
“However, this method has a significant drawback: each malware sample must contain a bot token for authentication. Decrypting the malware to extract this token provides access to all data sent through the bot, revealing the recipient’s account.”

The disclosure comes amid the emergence of new strains of malware such as Aylurafil, The Banshee Kidnapperand QWERTYdespite the fact that known hijackers such as RedLine are used in phishing attacks targeting Vietnam’s oil and gas, industrial, electrical and ventilation, paint, chemical and hospitality industries.
“RedLine is a well-known heist that uses login credentials, credit card details, browser history and even cryptocurrency wallets,” said Broadcom-owned Symantec. said. “It is actively used by various groups and individuals around the world.”
“Once installed, it collects data from the victim’s computer and sends it to a remote server or Telegram channel controlled by the attackers.”