It was found that the emergence of deformation of the ransomware, which includes the possibilities for file encryption, and constantly erase them, development, which has been described as “rare dual threat”.
“Redemption has a” wiping mode “that constantly erases files, making the recovery impossible even if the ransom is paid”, Trend Micro Researchers Miistel Policarpio, Sarah Pearl Camology and Sophia Nilet Robles Robles – Note In a report published last week.
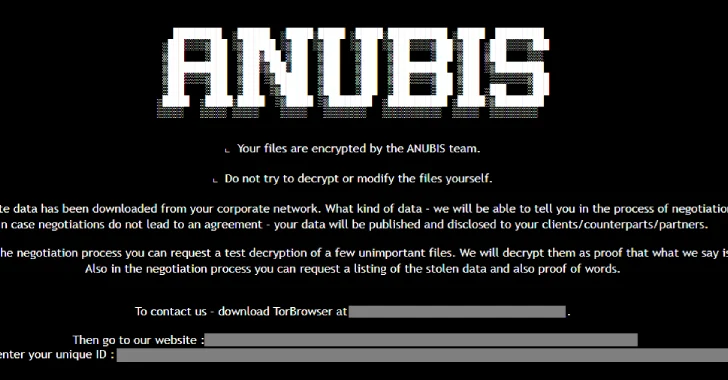
Operation Ransomware-How Service (RAAS), Named Anubis, which which became active In December 2024, stating that the victims across Sectors of health, hospitality and construction In Australia, Canada, Peru and the American analysis of the early trial samples of the ransomer, the developers initially called it a sphinx before setting up a trademark in the final version.
It should be noted that the electronic crimes crew has no connection with Android Banking Trojan and Based on python back Of the same name, the last of which is explained by the financially motivated Fin7 group (aka Grayalpha).
“Anubis manages a flexible affiliate program, offering revenue negotiation and supporting additional monetization ways such as extortion and access sale,” the cybersecurity campaign said.
The affiliate program stems from a split 80-20, allowing partners to take 80% of the paid rans. On the other hand, data extortion and monetization schemes offer a mixture of 60-40 and 50-50.
The anubis attack networks provide for the use of phishing sheets as a vector of the original access, with the threat to the threat use fixing to escalate the privileges, to conduct intelligence and to take measures to remove the volume of shadows before using the files and if necessary to wipe their contents.
This means that the file dimensions are reduced to 0 KB, leaving the file names or their expansion intact, making the restoration impossible, and thus put more pressure on the victims to pay.
“Redemption includes the Wiper feature using parameters /Wipemode, which can forever delete the contents of the file by preventing any restoration attempt,” the researchers said.
“His ability to both encrypt and constantly destroy data significantly increases rates for the victims, enhancing the pressure on the implementation – just as to seek ransom operations.”
The opening of devastating behavior Anubis occurs when recorded in the future detailed new infrastructure associated with the Fin7 group deliver the rat ntsupport.
Over the past year, the threatening firm owned by MasterCard has stated that three unique distribution vectors have been discovered over the last year Tag-124 (AKA 404 TDS, Chaya_002, Kongtuke and Landupdate808) for delivery of malware.
While the fake browser upgrade method is uploaded by a custom loader called Maskbat to perform the remote access, the other two vectors use another PowerShell loader, which is called Powernet, which decompresses and performs it.
“(Maskbat) has similarities Post But called and contains lines associated with graylof “, recorded by the Insikt Group of a future future – Note. “Although all three vectors of the infection were observed simultaneously, only fake 7-ZIP download pages are still active while writing, recently registered domains appeared recently in April 2025.”