Chinese aligned in China Group advanced permanent threat (APT) called Thewizards was associated with a side movement tool called Spellbinder, which can alleviate enemy attacks in the middle (AITM).
“Spellbinder allows the opponents on average (AITM) attack via IPv6 Ardess Autoconfiguration (Vine) forgeryTo move in lateral mode in the broken network, intercepted packages and redirecting the traffic of the legitimate Chinese software to load malicious updates from the server controlled by the attackers, “Eset Facundo Muñoz – Note In a report that shared with Hacker News.
The attack opens the way for the malicious bootloader, which is delivered by hijoking the software upgrade related to Sogou Pinyin. The bootloader then acts as a pipeline to give up a modular rear code called Wizardnet.
This is not the first time Chinese threatening subjects abused the Sogou Pinyin software update process to deliver their own malicious software. In January 2024, ESET spoke in detail about the hacking group called as Black tree This unfolded an implant called NSPX30, using the software upgrade mechanism to enter input methods.
Then earlier this year, the Slovak Cybersecurity Company revealed another cluster threats known as Plushdemon This used the same technique to distribute a custom bootloader called LitTledaemon.
As you know, TheWizards aims both in individuals and gambling in Cambodia, Hong Kong, mainland China, the Philippines and the United Arab Emirates.
The data suggest that the AITM Spellbinder IPV6 tool was used by an actor at least 2022. While the accurate initial access vector used in the attacks, at this stage, the unknown, successful access is accompanied by the Shipping Archive, which contains four different files: avgapplicationframehost.exe, wsc.dll, log.dat and winpcap.exe.
Then the actors threatens continue to install “Winpcap.exe” and launch “Avgaplicationframehost.exe”, the latter of which is abused to download Dll. Later, the dll file reads Shellcode with “log.dat” and performs it in memory, resulting in the process of the Spellbinder.
“Spellbinder uses Library Winpcap To capture the packages and respond to the packages if necessary, ”Munos said.
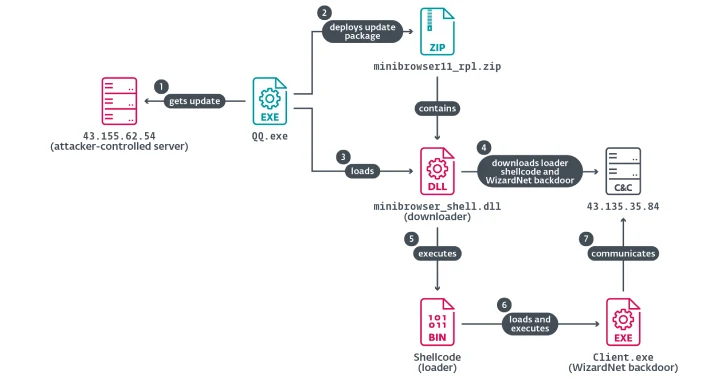
In one case of the attack, which is observed in 2024, the threat subjects used this method to kidnap the Tencent QQ software upgrade at the DNS level to maintain the trajonized version, which then unfolds the Wizardnet, a modular back that is equipped and launch. Net load on the infected host.
Spellbinder shoots this by intercepting the DNS request for the software update domain (“update.browser.qq” (.) COM “) and issuing a DNS server’s IP address controlled by the attacker (” 43.155.62 (.) 54 “), conducts.
Another characteristic tool in Thewizards Arsenal – these are the dark nights, also called Darknimbus Trend Micro and was attributed to another Chinese hacking group tracked as Land minotaur. Given this, both clusters are regarded as independent operators, citing differences in instruments, infrastructure and targeted in the footsteps.
This has since conclusion The fact that the contractor of the Ministry of Public Security Nickname Sichuan Dianke Network Security Technology Co., Ltd. (he aka UPSEC) is a provider of Darknimbus malicious software.
“While TheWizards uses another back for Windows (Wizardnet), the abduction server is tuned to maintain dark legs for Android -devils upgrading,” Munos said. “This indicates that Dianke Network security is a digital boss for TheWizards APT Group.”