North Korean threats behind a contagious interview have taken more and more popular Clickfix Social engineering tactics to attract people looking for work in the field of cryptocurrencies to deliver a previously unregistered back Go, called GolangHost in Windows and Macos Systems.
The new activity that is estimated throughout the campaign has been named Interview Clickfake French Cybersecurity Company SEKOIA. Increased interviewAlso monitored as deport development, Dev#Popper and the famous Chollima, is known, has been valid at least from December 2022, although it was only recorded for the first time in the late 2023.
“It uses legitimate web -residues to interview to use Clickfix tactics and install Backdoors Windows and MacOS,” – Researchers Sekoia Amaury G., Colin Chavane and Felix Aimé – Noteattributed to the efforts to shameful Group LazarusThe prolific opponent attributed to the General Bureau of Intelligence (RGB) of the Democratic People’s Republic of Korea (PRC).
The characteristic aspect of the company is that it is primarily aimed at centralized financial subjects, presenting itself by companies such as Coinbase, Kucoin, Kraken, Circle, Securitize, Blockfi, Tether, Robinhood and Bybit, noting (Defi).
Contagious interview like Operation Work Dreamsworks Fake job offers As baits to attract future goals and push them to download malware that can steal cryptocurrency and other sensitive data.
As part of the efforts, the candidates turn to LinkedIn or X to prepare for an interview video call, for which they are offered to download the video conferencing software laid on malware, or an open source project that activates the infection process.
Use Lazarus Group Tactics Clickfix was first revealed in late 2024. Taylor Monakhan’s security researchers, and the attack chains led to the deployment of the family malware called Ferret This then provides the back of Galan.
The company is invited to visit the alleged interview with the villa and complete the video assessment.
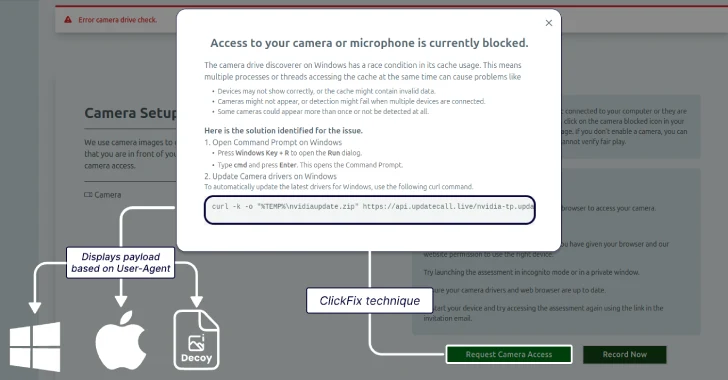
“The whole installation, carefully designed to create the confidence of users, continues until the user is asked to turn on their camera,” Socai explained. “At this point, an error shows that the user needs to download the driver to fix the problem. This is where the operator uses the Clickfix technique.”
The instructions given to the victims include access to the camera or microphone vary depending on the operating system used. The Windows Objectives are offered to open a team string and execute the CURL command to execute the visual basic script file (VBS), which then launches the package to launch the GolangHost.
In case the victim visits the site from the MacOS machine, they are similarly asked to launch the terminal application and run the Curl command to launch the shell script. The script of the malicious shell, for its part, launches the second shell scenario, which, in turn, performs the theft module called Frostyferret (aka ChromeupdateAlert) and the back.
Frostyferret reflects a fake window indicating that the Chrome web browser requires access to the camera or the user’s microphone, after which it displays a hint for entering a system password. The information entered, regardless of whether it acts or other, stands out to the Dropbox site, which is likely to indicate an attempt to access the iCloud key using a stolen password.
Golanghost is designed to facilitate remote control and theft through several commands that allow you to upload/download files, send information about the house and steal the web browser data.
“It has been found that all positions were not related to technical profiles in the development of the software,” Sekia noted. “They mainly occupy a manager, focusing on business development, asset management, products or specialized financing professionals.”
“This is a significant change compared to previous documented companies related to DPRK-NEXUS threatens, and on the basis of fake interviews, which are mainly aimed at developers and software engineers.”
IT -WIPS SCHEMS North Korea becomes active in Europe
Development comes when Google Intelligence Group (Gtig) said she watched the splash in The deceived IT -Working Scheme In Europe, emphasizing a significant expansion of its activity outside the US.
IT -workers’ activity entails North Korean citizens who represent legitimate remote workers to penetrate companies and receive illegal income for Pyongyang Violation of international sanctions.
Increased awareness activity combined with COLDS OF THE Ministry of Justice of the USAThey started a “global expansion of IT labor operations,” Google said, noting that he had discovered several fabricated characters looking for work in various organizations located in Germany and Portugal.
IT workers also watched various projects in the United Kingdom related to the development of the web internet, the development of the bot, the development of the content control system (CMS) and the Blockchain technology, often falsify their identity and state that from Italy, Japan, Malaysia, Singapore, Singapore.
This is the tactics of IT -workers who acted as Vietnamese, Japanese and Singaporean citizens isolated Managed Nisos intelligence firm at the beginning of last month, and also indicates the use of GitHub to cut new characters or process the content of the portfolio from old characters to strengthen their new ones.
“IT -workers in Europe were enrolled through various online platforms, including upwork, telegram and freelancer,” Jamie Coler, leading advisor for threats in GTIG, GTIG, – Note. “Payment for its services was facilitated by cryptocurrency, transfer and Payoneer service, emphasizing the use of methods that make it difficult to origin and purpose.”
In addition to using local facilitators to help them land, the insider threat is witnessing what seems to be a thorn attempts to extort Since October 2024, when it became a public knowledge that these IT workers have resorted to payments from their employers to prevent them from releasing their own data or provide them with a competitor.
The fact that it appears to be the further evolution of this scheme, IT workers are said to be focused on companies working in the “acceptance of their own device” (byod) because such devices are unlikely to be traditional security tools and registrations used in the enterprise environment.
“Europe needs to wake up quickly. Despite the fact that IT labor operations are, too much perceives it as a problem in the United States. The latest changes in North Korea are likely to emerge from US operational obstacles, showing IT workers and the ability to adapt to changing circumstances,” Kolier said.
“The decade of various cyberators is preceded by the last surge of North Korea – from Swift Targeting and Ransomware, to the theft of cryptocurrency and compromise supply chain.