Hated hunters warn of the complex Company Web Skimmer This uses an outdated application programming interface (API) with a payment processor to check the stolen payment information before exclusion.
“This tactic guarantees that the attackers are sent only valid card data, making the operation more efficient and potentially more difficult to detect,” – JSCrambler Pedro Fortuna, David Alves and Pedro Marrucho Researchers – Note In the report.
49 merchants estimate have been hit by the company today. Fifteen compromised sites have taken steps to remove malicious scenarios. Activity is estimated as at least on August 20, 2024.
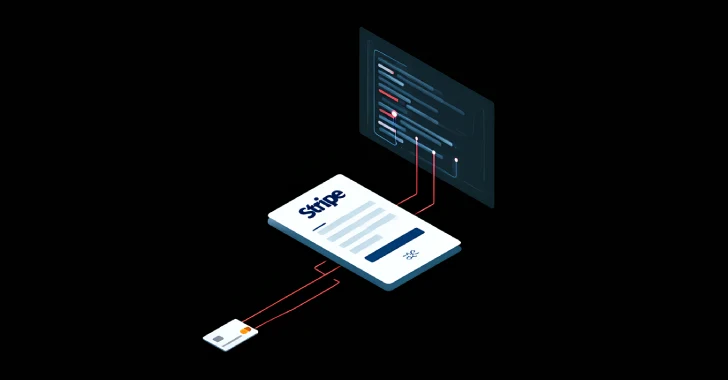
The details of the company were First specified Protecting a security source at the end of February 2025, which details the use of the Internet “API.Stripe (.) Com/v1/source“API, which allows applications to take different ways of payment. Since then, the final point has been outdated in favor of the new API PaymentmetHods.
The attack networks use malicious domains as the initial distribution point for Skimmer JavaScript, which is designed to intercept and hide the legitimate payment form on the order pages, maintenance of the leg of the legal strip, check it using the API sources, and then transmit it to the removed server in the base 64.
JSCRAMBERER said the threats behind the operation are most likely to use vulnerabilities and incorrect settings in WooCommerce, WordPress and Prestashop to implant the initial stage. This loader’s scenario serves to decipher and launch the next Base64 stage, which in turn contains the URL that points to the skimer.
“The Skimmyming scenario hides the legitimate IFRAM lane and blocked it with an angry, intended for imitation of its appearance,” the researchers said. “It is also to put the” order place “button, hiding the real one.”
Once the details are highlighted, the user shows an error message, asking them to restart the pages. There are several evidence that suggests that the final carimens are generated using some tools because the scenario appears to be given each target site.
In addition, the safety company noted that it revealed the scripts of Skimer, which represent itself for the square form of payment, believing that the threat subjects are likely to focus on several payment services providers. And that’s not all. There was also an observed descent code that adds other payment options using cryptocurrencies such as Bitcoin, Ether (Ethereum), Tether and Litecoin.
“This complex viewing company emphasizes the developing tactics that the attackers use to go unnoticed,” the researchers said. “And as a bonus, they effectively filter unacceptable credit card data, ensuring that only the valid credentials have stolen.”