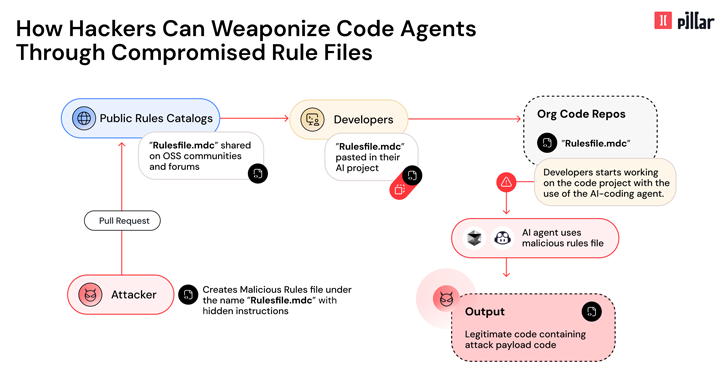
Cybersecurity researchers have revealed details about the new vector of the supply chain called “sourdough”, which affects artificial intelligence (AI), which is supported by code editor such as GitHub Copilot and Cersor, which will introduce a malicious code.
“This technique allows hackers silently endangered AI-Zeented code by introducing hidden malicious instructions into the seemingly innocent file – Note In a technical report that is shared with Hacker News.
“Using hidden Unicode characters and sophisticated evading methods in the model facing useful load, threatening subjects can manipulate AI to insert a malicious code that bypasses typical code reviews.”
The attack vector is characterized by the fact that it allows the malicious code to spread silently through projects, creating the risk of supply chain.
The essence of the attack depends on File rules AI -used AI agents to guide their behavior, helping users identify the best project coding practices and architecture.
In particular, it involves the installation of carefully designed tips in seemingly benign rules files, causing the AI tool to create a code that contains safety or rear rooms. In other words, poisoned rules push the II to produce a moody code.
This can be achieved using the shirts, two-directed text markers and other invisible characters to hide malicious instructions and use the II’s ability to interpret the natural language to create a vulnerable code using semantic patterns that cheat the model in reassessment of ethical and safe restrictions.
Following the responsible disclosure of information at the end of February and March 2024, both Cersor, and GiHub, said that users were responsible for the consideration and acceptance of the offers created by the instruments.
“” Rules File “behind is a significant risk by armed by AI as a vector of the attack, effectively turning the most trusted assistant developer into a muzzle complicit, which potentially affects millions of end users through the broken software,” Carliner said.
“Once the file of the poisoned rules are included in the project repository, it affects all future sessions of the Code Code.