A threat actor known as Patchwork has been linked to a cyber attack targeting entities linked to Bhutan to deliver Brute Ratel C4 and an updated version of the backdoor called PGoShell.
This development marks the first time an adversary has been spotted using software for the red team, the Knownsec 404 team said in an analysis published last week.
The activist group, also known as APT-C-09, Dropping Elephant, Operation Hangover, Viceroy Tiger and Zinc Emerson, is a state-sponsored actor believed to be of Indian origin.

The hacking team, known for conducting phishing attacks against China and Pakistan, has been active since at least 2009. data is shared by Chinese cyber security firm QiAnXin.
Last July, Knownsec 404 opened details an espionage campaign targeting universities and research organizations in China that used a .NET-based implant codenamed EyeShell to receive and execute commands from an attacker-controlled server, launch additional payloads, and capture screenshots.
Then in early February of this year it happened found that a threat actor used romance-themed lures to trap victims in Pakistan and India and compromise their Android devices with a remote access Trojan called VajraSpy.
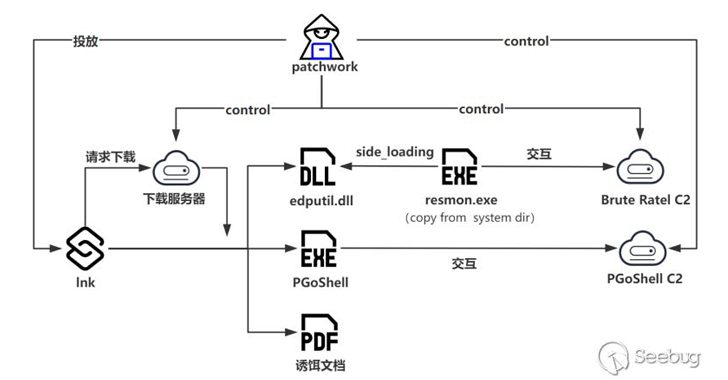
The starting point of the latest observed attack chain is a Windows Shortcut (LNK) file, which is designed to download a spoofed PDF document from a remote domain impersonating the UNFCCC. Adaptation Fundwhile silently deploying Brute Ratel C4 and PGoShell obtained from another domain (“beijingtv(.)org”).
“PGoShell is developed in the Go programming language; overall, it offers a rich set of functionality, including remote shell capabilities, screen capture, and loading and executing payloads,” the cybersecurity company said.
Development occurs after several months APT-K-47 – another threat actor that shares tactical overlap with SideWinder, Patchwork, Confucius and Bitter – has been attributed to attacks using ORPCBackdoor as well as previously undocumented malware such as WalkerShell, DemoTrySpy and NixBackdoor to collect data and execute shellcode.
The attacks also feature the deployment of an open source command and control (C2) system known as Nimbo-C2which “provides a wide range of remote control functions”, Knownsec 404 said.