Ukraine’s Computer Emergency Response Team (CERT-UA) has warned of a phishing campaign targeting a research institution in the country with malware known as HATVIBE and CHERRYSPY.
Agency attributed to it tracks an attack on a threat actor by name UAC-0063which has previously been seen targeting various government entities to collect sensitive information using keyloggers and backdoors.
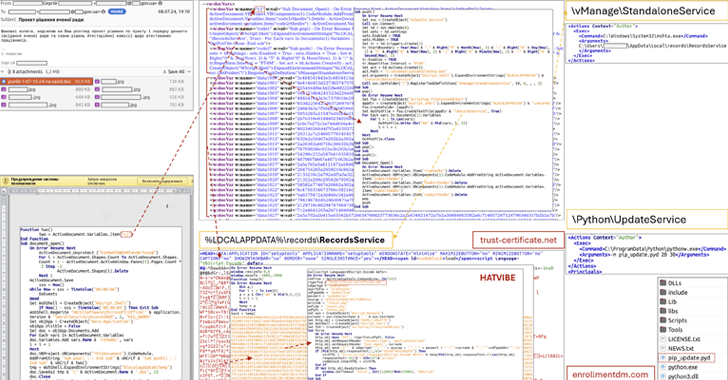
The attack is characterized by the use of a compromised email account belonging to an employee of the organization to send phishing messages to “dozens” of recipients containing a Microsoft Word (DOCX) attachment with macros.
Opening the document and enabling the macros results in the execution of an HTML Encoded Application (HTA) called HATVIBE, which configures security on the host via a scheduled task and opens the way for a Python backdoor, codenamed CHERRYSPY, which is capable of running commands issued by a remote server.

CERT-UA said it found “multiple instances” of HATVIBE infections exploiting a known security flaw in the HTTP file server (CVE-2024-23692CVSS score: 9.8) for initial access.
UAC-0063 has been linked to a Russia-linked nation-state group called APT28 with moderate confidence. APT28, also known as BlueDelta, Fancy Bear, Forest Blizzard, FROZENLAKE, Iron Twilight, ITG05, Pawn Storm, Sednit, Sofacy, and TA422, is linked to Russia’s strategic military intelligence unit, the GRU.
The development is delivered as CERT-UA in detail another phishing campaign targeting Ukrainian defense companies with mined PDF files embedded in a link that, when clicked, downloads an executable file (aka GLUEEGG) responsible for decrypting and running a Lua-based bootloader called DROPCLUE.
DROPCLUE is designed to open a decoy document for the victim while secretly downloading a legitimate remote desktop program called Atera Agent using the curl utility. The attack was linked to a cluster tracked as UAC-0180.